Share this
5G Edge Computing: What You Need to Know
by Christopher Trick on May 6, 2022 10:54:31 AM

Across a wide range of industries, 5G technology is being adopted to enable local data management and rapid data transfer.
In this blog, you'll learn more about what 5G is and how it utilizes high-performance edge computing to enhance AI applications closer to the source of data.
What is 5G?
5G is the fifth-generation technology standard for broadband cellular networks. It is the successor to 4G technology, which is widely used today.
Most importantly, 5G utilizes software-defined networks (SDNs), which virtualize controllers to enable the management and routing of data packets via a centralized server, eliminating the need for expensive hardware.
Because of this, 5G is able to deliver high data transfer rates, reliability, low latency, massive network capacity, and increased availability to enhance connectivity, creating a more uniform experience for all users. And with less hardware to be compromised, data is routed through virtual hubs that can be moved or changed quickly if required.
Differences from 4G Technology
There are some key differences between 5G and 4G technology:
- 5G is much faster than 4G (up to 10 Gpbs, peak data rate, and 100+ Mbps, average data rate) vs. 1 Gbps on 4G.
- 1 ms latency vs. 10 ms on 4G.
- 5G has a much higher capacity, about 100x over 4G along with a much better network efficiency.
- 5G can support all spectrum types (licensed, shared, unlicensed) and bands (low is below 1 GHz, mid is 1 GHz to 6 GHz), high or millimeter wave (mmWave), a wide range of deployment models (macro-cells to hotspots), and new ways to interconnect (device-to-device and multi-hop mesh).
- 5G is 90% more efficient which offers a drastic battery life improvement, which is very important for mobile devices.
How does 5G work?
5G NR (New Radio) air interface will further enhance OFDM to deliver much higher flexibility and scalability.
The future of 5G
By 2025, 5G is expected to have more than 1.7 billion subscribers, indicating that the technology is growing in popularity among the public and private sectors.
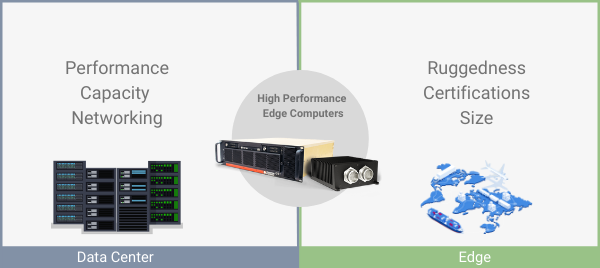
To fully enable the power of 5G, however, there is a need for an infrastructure of nodes (servers/computers) to run AI (artificial intelligence) applications at the edge, meaning closer to the data source, and allow local management of data.
This is where high-performance computers come into the mix. Let's take a closer look.
5G Technology and High-Performance Edge Computers
Purpose
Simply put, edge computing means that data is processed near the source.
With regular computing, data is usually sent from a device to a centralized data center for processing and is then sent back to the device.
Edge computing speeds up the process by bringing server and data-center capabilities such as computing power, storage capacity, and network bandwidth into computing devices. Additionally, processing data closer to the source makes threat detection much easier.
This is especially useful in military environments, as warfighters often need immediate, actionable insights to increase situational awareness and effectively track enemy threats, so they can deliver decisive action in minimal time.
For military and commercial purposes, bringing these capabilities to the edge means customizing ruggedized, SWaP-C optimized computing solutions to comply with a myriad of technical, performance, and environmental specifications in order to ensure reliable performance in the harshest of environments.
Edge computing speeds data processing by bringing server and data-center capabilities such as computing power, storage capacity, and network bandwidth into computing devices.
Operating as edge nodes, high-performance computers possess enhanced computing, data logging, and networking capabilities to run multiple virtualized applications and RAN (radio access network) infrastructures on the same piece of hardware.
RAN is a network infrastructure consisting of radio base stations with large antennas that receive, process, convert, and transmit radio signals to be forwarded to the core network.
vRAN, or virtualized RAN, is a critical component of 5G technology, as it virtualizes hardware functions to increase automation, flexibility, and adaptability in response to changing network conditions.
This is especially useful as devices become more interconnected in an Internet of Things (IoT) and the amount of data generated on a daily basis by these devices and others has increased exponentially.
How does Trenton fit in?
5G technology brings some challenges when it comes to integrating with existing infrastructures and managing massive amounts of data, further highlighting the need for reduced latency in mission-critical applications.
Our hardware provides computing power, storage capacity, and network bandwidth to manage the huge amounts of data 5G is going to generate from an increasing number of sensors and devices.
 1U BAM FM
1U BAM FM
A ruggedized, secure, USA-made modular blade server with extensive configurability to enhance AI/ML/DL workloads at the edge in real-time.
 3U BAM
3U BAM
A ruggedized, SWaP-C optimized rack mount server for high-performance edge computing and AI inferencing across the modern battlespace.
Besides reducing latency and offloading traffic from the core network, our systems help to improve connectivity through supporting 5G technology, eliminate expensive hardware through virtualization capabilities, and enable remote management through IPMI, reducing total cost of ownership.
Extremely lightweight and modular, we also enable quick mounting and rapid deployment in the field, reducing downtime and ensuring optimal performance.
Applications and Use Cases
On the whole, 5G connectivity will transform the way that the military operates by connecting sensors and weapons to help warfighters better understand, shape, and adapt to complex and congested physical and information environments.
The ultimate goal of 5G for the military is to deliver real-time intelligence, creating an infosphere where data from sensors, targeting, surveillance, and signals is readily available.
Let's take a look at some potential applications and use cases.
Electronic Warfare (EW)
A core component of EW is to use signals to attack the enemy and make sure they cannot disrupt or use these signals themselves.
Pairing a 5G network that operates in very high frequency (millimeters) with supported waveforms that have very little probability of detection provides a competitive advantage.
Additionally, 5G networks avoid disruption from accidental or purposeful signals that get in the way, and even if there was any sort of disruption, other 5G-powered technologies could aid in identifying it.
Unmanned aerial vehicles (UAVs)
UAVs need to stay in constant contact in order to change their performance accordingly and navigate through congested air space.
Through enhanced connectivity and lower latency, 5G enables UAVs to communicate instantly by sending real-time data to other vehicles, controllers, and users, even in areas with limited connectivity.
Therefore, UAVs can fly BVLOS (beyond visible line of sight), as they are able to provide real-time insights into their environment, quickly receive and act upon commands sent from a pilot or ground control system, and, if need be, amend their course of action.
For example, drones can provide a view of current battlefield conditions and feed control rooms the necessary data to prompt an immediate response, reducing the margin of error.
Drones can also give insight into current levels of air traffic and weather conditions, leading to fewer collisions and preserving functionality.
C4ISR (Command, Control, Communications, Computers, Intelligence, Surveillance, Reconnaissance)
C4ISR systems require increasingly high bandwidth to process, analyze, and distribute intelligence from a network of ground and aerial sensors.
Coupled with AI, 5G can provide commanders with timely access to key intelligence and actionable insights that enhance situational awareness and reduce decision-making times.
For example, let's say an ICBM (intercontinental ballistic missile) is headed for the United States. 5G will be able to provide command room personnel with the insights necessary to effectively track and destroy the missile within a matter of seconds.
Final thoughts
At its core, 5G technology aims to create ubiquitous communications with a global network to drive AI processing and operational decisions to the edge, increasing situational awareness, reducing decision times, and ensuring optimal performance.
5G communications systems bring more reliable, higher throughout, secure, and ultra-low-latency connectivity required for edge devices and platforms to fully harness the power of AI and deliver prompt, decisive action across all domains of the modern battlespace.
By integrating 5G with existing military communications, warfighters can achieve more effective operations in the harshest of environments and have access to data to perform their missions anywhere in the world.
Interested in learning more about 5G? Check out some other key 5G technologies that enhance compute architectures here.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)
No Comments Yet
Let us know what you think