Share this
MIL-STD-810 Sand & Dust Testing Overview [Method 510.7]
by Brett Daniel on May 20, 2020 3:45:54 PM
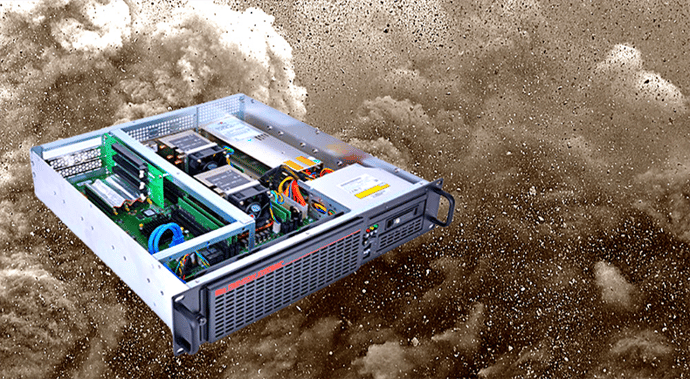
Graphic: Test method 510.7 of MIL-STD-810 may be worth looking into if your rugged server is expected to operate in arid or semi-arid regions.
Note: Trenton Systems is not a compliance testing facility. We manufacture rugged servers and workstations that conform to military and industrial standards, such as MIL-STD-810 and DO-160, and we can ensure that our systems comply with these standards using our in-house testing equipment, or by sending our systems to a third-party compliance testing laboratory for validation, but our facility does not offer compliance testing services for products manufactured outside of Trenton Systems. For a list of laboratories that can assist you with your testing needs, please read this blog post, which lists the best compliance testing laboratories in the world.
This is Part 3 in a series of the different test methods in MIL-STD-810H, the successor to MIL-STD-810G. View Part 2: Vibration Testing and Part 1: Temperature Testing.
Having your rugged server certified to MIL-STD-810 standards is one of the best ways you can ensure its survival and functionality in the field.
When looking for the perfect military computer for your program or application, it’s important to be aware of the different locations and environments in which it will ultimately operate.
That way, you’ll know which specific military certifications to ask about when you’re shopping around.
Sand and dust testing, along with temperature, vibration and humidity testing, is one of the more common rugged computer test methods out there.
It’s often used when a system is expected to operate in arid or semi-arid regions, where sand and dust storms commonly occur, or where aircraft are likely to propel sand particles into the air during takeoff, hovering or landing.

Photo: Helicopters are known for propelling desert sand into the air upon takeoff and landing.
What is MIL-STD-810 sand and dust testing?
According to MIL-STD-810H, sand and dust testing, also known as MIL-STD-810H-510.7 or simply Test Method 510.7, is performed to evaluate the resistance of a system to dust and sand particles, which may obstruct openings and penetrate cracks, crevices, bearings and joints.
The standard defines dust as particulates less than 150 micrometers, or 0.00590551 inches, in diameter, while sand is defined as particulates 150-850 micrometers, or up to 0.0334646 inches, in diameter.

Important figures associated with environmental stand and dust testing. Infographic by Trenton Systems
How is sand and dust testing performed?
Environmental sand and dust testing is performed by placing a system into a blowing chamber and exposing it to sand or dust particles while controlling for temperature, relative humidity, air velocity, particle composition, particle concentration and system orientation.
The harmful effects of sand and dust exposure on a system include:
- Abrasion and erosion of surfaces
- Penetration of seals
- Degradation of electrical circuits
- Obstruction or clogging of openings and filters
- Physical interference with mating parts
- Fouling or interference of moving parts
- Reduction of thermal conductivity
- Interference with optical characteristics
- Overheating and fire hazard due to restricted ventilation or cooling
- Wear (increased fretting due to embedding between mating surfaces)
- Increased chaffing between non-mating contact surfaces
- Weight gain and static or dynamic balance
- Attenuation of signal transmission
What are the sand and dust testing methods?
There are two sand and dust testing methods or procedures:
- Procedure I – Blowing Dust
- Procedure II – Blowing Sand
Procedure I – Blowing Dust
Procedure I – Blowing Dust involves exposing a system to circulating dust particles, preferably from the region in which the system is expected to operate, for 12 hours.
If natural dust from the specific region is not available, a test dust closest in composition can be used.
Temperature conditions should be kept at standard ambient air temperatures, as well as the system’s previously established high operating and storage temperatures.
Relative humidity should not exceed 30 percent due to the caking of particles that occurs in particularly humid environments.
Air velocity should be 300 +/-200 feet/minute to maintain test temperature conditions and increased to 1750 +/-250 feet/minute to effectively simulate desert winds.
Other air velocities can be used to represent the system’s intended environment.
The system in question is operated during testing if it is intended to operate during a real-world dust event.
Damage and impairment are also assessed once testing concludes.
Procedure II – Blowing Sand
Procedure II – Blowing Sand involves exposing a system to particles of quartz sand resembling those in the region of interest for 90-minute intervals.
Given that there are 90 deserts across the globe, each with different sand particle size distributions, it is impossible to determine a distribution that accounts for every locale, which is why the standard 150-850 micrometer particle size is used during testing.
If a system is expected to operate in a region with an unusual sand composition, samples should be collected and analyzed to determine the distribution of the material used to stress-test the computer.
Temperature conditions should be kept at standard ambient air temperatures, as well as the system’s previously established high operating and storage temperatures.
Air velocity should be 18-29 m/s, or 40-65 mph, to simulate real-world wind and wind gusts, as well as ensure that the particles remain suspended during circulation.
The system should be reoriented at 90-minute intervals so that it can experience maximum erosion effects.
The system in question is operated during testing if it is intended to operate during a real-world sand event.
-5.png?width=1000&name=Untitled%20design%20(9)-5.png)
Graphic: The desert can be a harsh place for rugged computers. Avoid the headache by having your system MIL-STD-810-certified.
Should your system be tested for sand and dust exposure?
MIL-STD-810 sand and dust testing is perfect for systems expected to survive and function in dry, hot regions, such as any one of the 90 deserts in the world.
Sand and dust testing won’t be necessary if your system is to be located somewhere humid, rainy or in any other environment where dust storms, sandstorms and aircraft-generated exposure are neither common nor cause for concern.
If you expect that you’ll encounter any of the above, then for the sake of your system and your wallet, ask your rugged computer manufacturer about sand and dust testing.
After all, severe damage to your server or workstation isn’t just something you can dust off.
Trenton Systems tests its servers and workstations to military and industrial standards in-house and maintains relationships with local compliance testing labs to test and certify our made-in-the-USA rugged computers to various military and industrial standards.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)

No Comments Yet
Let us know what you think