Share this
JBOD vs. RAID: What Are the Differences?
by Brett Daniel on May 1, 2020 3:40:25 PM
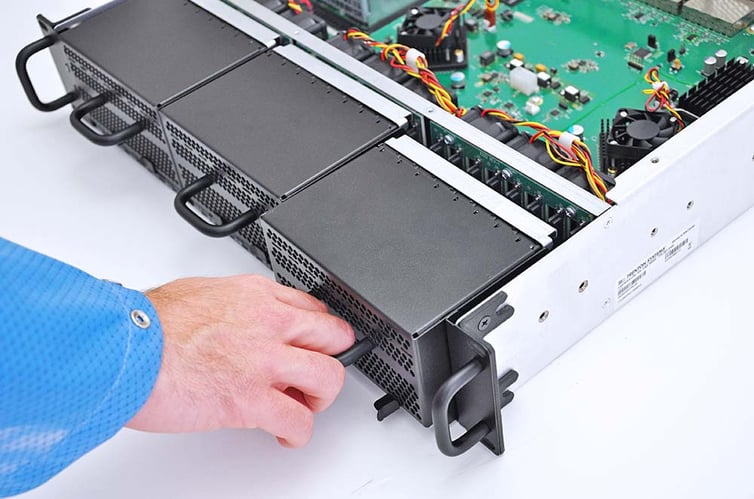
Photo: The basic difference between a JBOD enclosure and RAID is that the former is a collection of storage drives, while the latter is a storage technology used to improve read and write speeds or fault tolerance. In this blog post, we'll discuss these differences a bit more.
We’ve talked about the different RAID levels before.
Aside from RAID 0, often employed for its fast read and write speeds, the various RAID levels satisfy unique data redundancy needs. The level that a program or application utilizes will depend upon its speed and fault tolerance requirements.
JBOD, although it shares some similarities with RAID, is a different animal altogether.
So, what is JBOD, and how is it different from RAID?
Well, when it comes to JBOD, the name pretty much says it all.
What is JBOD?
JBOD, which stands for Just a Bunch of Disks or Just a Bunch of Drives, is a storage architecture consisting of numerous disk drives inside of a single storage enclosure.
JBOD enclosures are usually not configured to act as a RAID, but they can be.
By their very nature, JBOD enclosures are storage capacity monoliths.
The ruggedized 3MAG JBOD, for example, is equipped with 24 8TB solid-state drives per magazine, which amounts to a whopping 192TB of storage. The space, speed and rugged characteristics of this particular enclosure make it ideal for big data applications and local storage.
The drives in a JBOD enclosure can function as individual units, undergo disk spanning to act as one unit or be configured to act as a RAID with the right host system technology.
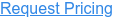
Photo: RAID 0, the simplest of all RAID levels
What is RAID?
Redundant Array of Independent Disks (RAID) is a storage technology that creates a data loss fail-safe by merging two or more hard disk drives (HDDs) or solid-state drives (SSDs) into one cohesive storage unit or array.
There are many different RAID levels, but the most common are RAID 0, RAID 1, RAID 5, RAID 6 and RAID 10.
| RAID Configurations: Processes and Fault Tolerance | |||||
| Raid Level | Raid 0 | Raid 1 | Raid 5 | Raid 6 | Raid 10 |
| Process | Data Striping | Disk Mirroring | Striping + Parity | Striping + Double Parity | Mirroring + Striping |
| Tolerance | Not Fault-Tolerant | Fault-Tolerant | Fault-Tolerant | Fault-Tolerant | Fault-Tolerant |
RAID storage protects against the total loss of a disk drive’s data by repeating or recreating that data and storing it on the additional drive or drives, a process also known as data redundancy.
How does JBOD compare to RAID?
JBOD and RAID use different processes to store data.
When functioning as one unit, JBOD uses a process called spanning. When one disk drive in the enclosure reaches its capacity, data is stored on the next drive in the enclosure, and so on throughout the entire unit. Data is not fragmented, duplicated or combined as with RAID.
The various RAID levels use a variety of storage processes to achieve data redundancy and fault tolerance, including striping, mirroring, a combination of striping and mirroring, parity and double parity.
For example, RAID 0 uses striping only, which fragments data onto the drives in the array and offers no data redundancy, while RAID 1 uses mirroring only, which duplicates data onto the drives and offers data redundancy, albeit a less than outstanding degree of fault tolerance.
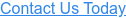
Photo: A Trenton Systems NVME JBOD Enclosure. Note the 24 individual NVME solid-state drives. This JBOD is perfect for programs and applications that need tons of storage and super fast read and write speeds.
Like RAID, JBOD enclosures can make use of both hard disk drives and solid-state drives of varying storage capacities and interfaces, including lightning-fast NVME SSDs, which Trenton Systems uses in its JBOD enclosures.
JBOD enclosures and most RAID levels allow for hot swapping, meaning a drive in the enclosure or array can be replaced without shutting down the host system.
This is especially useful in programs and applications where users need frequent access to data stored on various servers.
Shutting down an entire system for drive replacement increases organizational downtime, and in turn, decreases productivity.
In mission-critical programs and applications, significant downtime and decreased productivity may have catastrophic consequences, such as financial loss, public outcry, serious injury and even death.
JBOD vs. RAID: Which configuration is right for me?
If you need tons of local storage for your program or application, choose a JBOD enclosure.
When it comes to storage capacity for big data applications, the JBOD is a tough cookie to beat.
And when equipped with NVME SSDs, JBODs are fast as lightning, too.
With RAID, most RAID levels have storage capacity limits due to data that’s being mirrored or undergoing parity.
RAID 0 is the only level where total storage capacity isn’t sacrificed, but you also can’t remove disk drives in a RAID 0 array without losing all the data on each drive.
Talk about a nightmare!
If you’re looking for something hot-swappable, both JBOD enclosures and RAID typically have this covered, so no worries there.
Now, if you’re not one for complexity when it comes to data storage, as in, you just need a simple, affordable system that stores a ton of data, then a JBOD is right for you.
RAID technology has its advantages, but it’s notoriously complex and particularly expensive when you enter the world of hardware RAID. Not to mention, if a drive in a RAID array dies, the drive can take a long time to rebuild due to the procedural complexity of certain RAID levels.
Always take a detailed look at what your program or application needs storage-wise.
And when it calls for tons of storage, crazy fast read and write speeds and easy drive swap in a lightweight, rugged chassis, you know where to find us. Our rugged JBOD enclosures just might be the right choice for you.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)

Comments (1)