Share this
Counterfeit Electronic Parts: A Multibillion-Dollar Black Market
by Brett Daniel on Jul 27, 2020 4:36:07 PM

Photo: A pile of electronic waste, or e-waste
An estimated 15 percent of all spare and replacement electronic parts purchased by The Pentagon are counterfeit.
Fifteen percent may not sound substantial, but when you consider the consequences that bogus electronics could have on national security and American lives, suddenly, the stakes are amplified, and a seemingly unsubstantial 15 percent becomes an alarming statistic worthy of great attention, and more importantly, an effective solution.
The manufacture of counterfeit electric, electromechanical and electronic (EEE) parts isn’t a new problem for the rugged computing industry, but sadly, it’s a problem that continues to cost manufacturers billions, harm the livelihoods of working Americans and jeopardize critical national security initiatives.
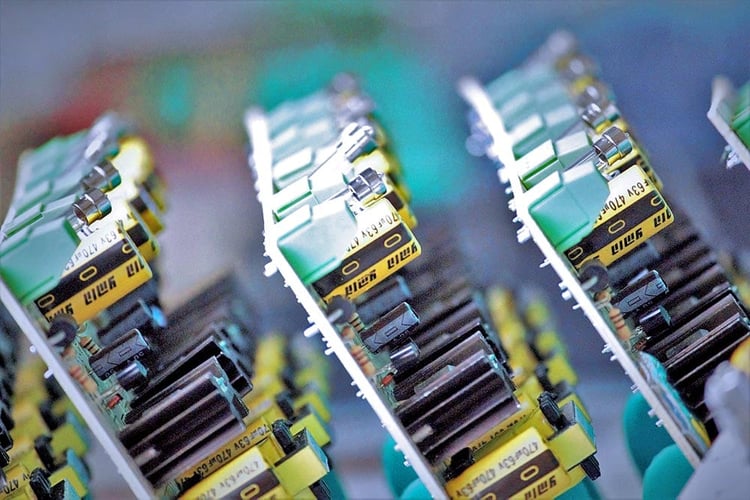
Photo: A collection of printed circuit boards
What is a counterfeit part?
A counterfeit part is an unauthorized copy, imitation, substitute or modified component that has been knowingly misrepresented as a legitimate component from an authorized manufacturer.
A counterfeit part can also be a used EEE component that has been altered and knowingly misrepresented as new without disclosure of its prior usage to the intended customer.
Parts are referred to as suspect when there is objective or credible evidence that a part is likely counterfeit.
What drives the purchase or usage of counterfeit parts?
There are a few contributing factors that enable the proliferation of counterfeit EEE parts in the industry, including:
- Multi-tiered supply chains
- Inadequate accountability practices
- Bargain hunting
- Scarcity of parts caused by end-of-life designations
- Assumption of quality control and testing by others
- Limited or inadequate inspection and testing resources
- Limited or inadequate record-keeping of counterfeit incidents
What are the consequences of using counterfeit parts?
The usage of counterfeit parts carries a high safety risk for military personnel and civilians, including severe injury and death, and can compromise the security, effectiveness and overall integrity of a manufacturer’s products, as well as destroy the victim manufacturer’s reputation.
Counterfeit electronic parts, particularly those that have been deceptively labeled as military-grade, have not undergone any sort of ruggedization testing for extremely high or low temperatures, shock, vibration, humidity or other conditions, and therefore do not meet the stringent requirements and standards for electronic parts deployed by the United States military. As a result, they are more likely to fail, putting the nation's critical infrastructure and innocent American lives at risk.
There are also financial and economic consequences associated with the sale and usage of counterfeit electronic parts.
The Semiconductor Industry Association (SIA), a trade group working to advance the policies and interests of American semiconductor companies on Capitol Hill, estimates that counterfeit parts cost manufacturers more than $7.5 billion annually. This translates into nearly 11,000 lost American jobs.
“The issue is of more and more importance as semiconductors are key components to an increasing number of mission-critical civilian applications, such as lifesaving medical devices, automotive safety systems, airplanes, but even more alarmingly, counterfeit semiconductors have infiltrated the tools, systems and communications equipment that our military is using today,” Brian Toohey, former president of SIA, told Congress in 2011 during a hearing by the Committee on Armed Services on the investigation of counterfeit electronic parts in the U.S. Department of Defense’s supply chain. “Given the high failure risk, this places our citizens and our military personnel in unreasonable peril. A counterfeit semiconductor is a ticking time bomb.”
Other consequences associated with the usage of counterfeit parts include:
- Premature system failures
- Loss of credibility with customers
- Increased root cause analysis
- Increased rework and repair
- Longer-than-necessary lead times
- Increased scrap
- Excessive inventories
Where do counterfeit parts come from?
There is no sole source of counterfeit electronic parts. Anywhere at any time, anyone with the knowledge and resources necessary to create counterfeit electronic parts, push them into the EEE parts supply chain and profit from their sale can do so. The origin of counterfeit parts, ergo, isn’t so much a matter of who or where, but a matter of how.
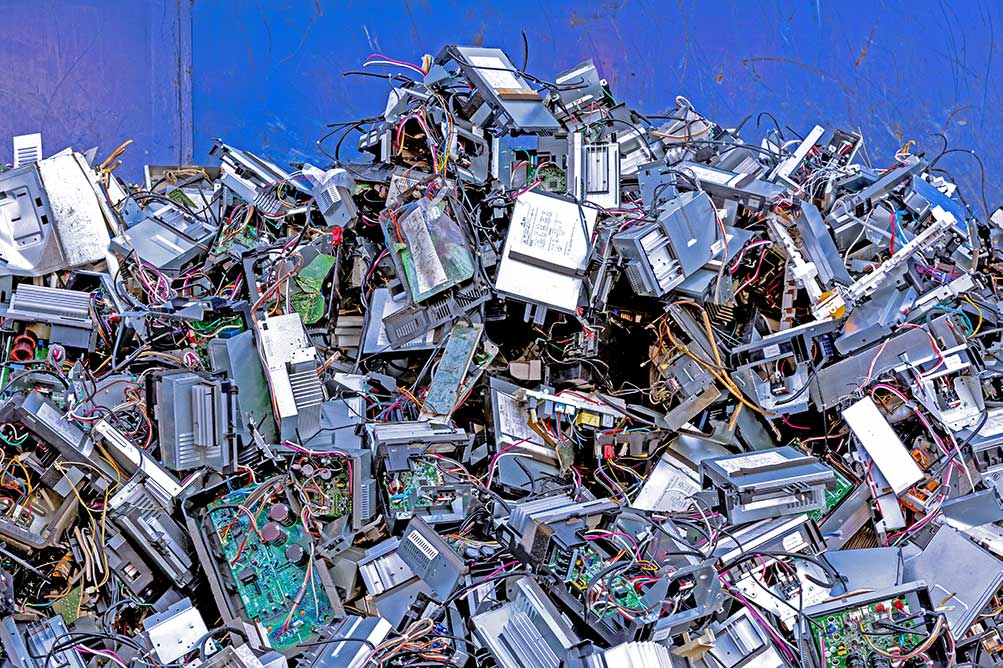
Photo: The creation of counterfeit electronics usually begins at an e-waste site.
How are counterfeit parts made?
A common method for counterfeiting electronic parts begins with the acquisition of legitimate discarded parts from piles of electronic waste. Some of these junk parts have been recently discarded, and others are decades old, meaning that some of these components, from the very moment they’re acquired, are destined to fail should they find themselves in modern equipment.
A variety of techniques, including surface sanding, acid washes, river washes and exposure to open flames, are then used to conceal the true origin of the part. Following the concealment process, the parts are often relabeled as military-grade using lasers and digital printing techniques, before being packaged and sold to brokers across the globe.
Another common method of counterfeiting electronic parts follows the same process of supply chain introduction; however, the parts, instead of being acquired from a pile of waste, are manufactured as blanks in a factory before being marked, packaged and sold.
Nine years ago, Toohey told Congress that these counterfeiting techniques were advancing and becoming more and more sophisticated, further decreasing the likelihood of manufacturers being able to accurately identify counterfeit parts in the supply chain.
As evidence, Toohey cited the infamous VisionTech case from 2010, during which Stephanie McCloskey, a then-administrator for VisionTech Components, LLC, was sentenced to more than three years in prison for assisting with the sale of hundreds of thousands of counterfeit integrated circuits, some of which were labeled as military-grade, to the U.S. Navy, major defense contractors and others.
McCloskey and her associates sold the fake parts, which they imported into the United States from Hong Kong and China using various ports of entry, on www.visiontechcomponents.com. Between 2007 and 2009, McCloskey and her associates generated approximately $15.7 million in gross receipts from the sale of these counterfeit integrated circuits.
McCloskey v. United States of America was the first federal case involving the trafficking of counterfeit integrated circuits.
The black market for counterfeit electronics continues to be a multibillion-dollar problem, and unfortunately, catching and prosecuting counterfeiters, particularly those operating in undisclosed locations outside of the United States, is an extremely difficult, time-consuming and expensive process. That's why prevention is always the first line of defense.
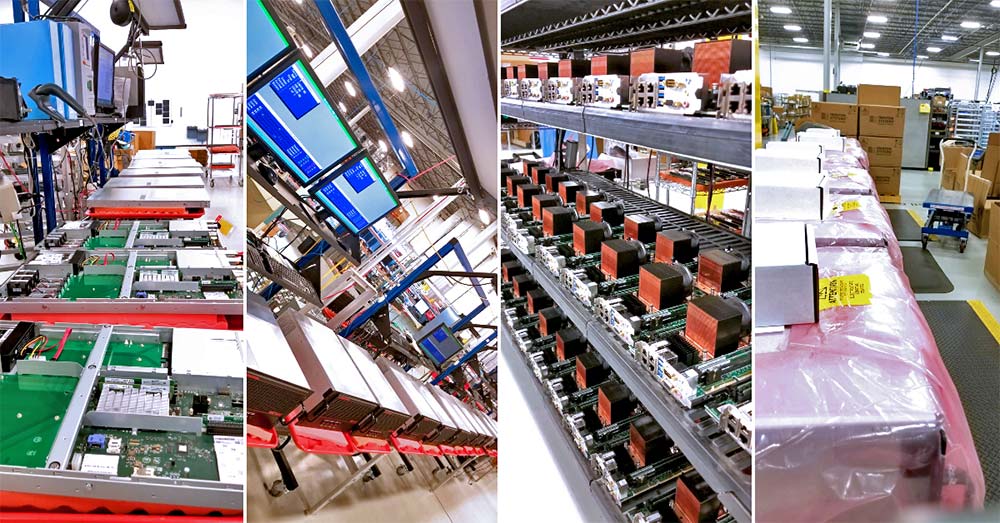
Photo: Trenton Systems has new and improved plans in place to prevent counterfeit part infiltration into its facility.
What is Trenton Systems doing to prevent infiltration?
Trenton Systems has always had preventative measures addressing counterfeit electronics in place. Recently, however, we implemented a new-and-improved counterfeit parts control plan, officially entitled the Counterfeit Protection Program, or CPP. At the core of the CPP is employee awareness and understanding of counterfeit EEE parts, how counterfeit EEE parts enter the industrial supply chain and how we, as a leading manufacturer of made-in-USA rugged computer hardware, can prevent infiltration.
“The purpose of Trenton Systems’ Counterfeit Protection Program, or CPP, is two-fold,” says Toni Lynn Hauck, Director of Quality at Trenton Systems. Hauck is responsible for CPP training, as well as drafting, implementing and ensuring adherence to the CPP. “We want to protect Trenton Systems and Trenton Systems’ customers from obtaining questionable parts, which could lead to extensive costs, delays and headaches. One way we can achieve this is by purchasing directly from original equipment manufacturers (OEMs), original component manufacturers (OCMs) or authorized distributors."
Hauck continues, “The quality and reliability of your products become compromised when counterfeit parts are found to have been introduced. It is Trenton's practice and primary intention to ensure the quality and reliability of our products, and to ensure customer purchase order and flow-down requirements are being met. In addition to annual training that has been tailored for each function within Trenton Systems, we have an active and ongoing membership with GIDEP as well as internal and external audits to ensure adherence to our CPP."
Most importantly, Trenton Systems’ new-and-improved CPP includes a more robust arsenal of inspection, detection, identification, documentation and certification techniques to minimize the risk of incorporating or shipping counterfeit parts.
For more information about the Counterfeit Protection Program (CPP), contact Trenton Systems at info@trentonsystems.com or 770-287-3100.
Share this
- High-performance computers (42)
- Military computers (38)
- Rugged computers (32)
- Cybersecurity (25)
- Industrial computers (25)
- Military servers (24)
- MIL-SPEC (20)
- Rugged servers (19)
- Press Release (17)
- Industrial servers (16)
- MIL-STD-810 (16)
- 5G Technology (14)
- Intel (13)
- Rack mount servers (12)
- processing (12)
- Computer hardware (11)
- Edge computing (11)
- Rugged workstations (11)
- Made in USA (10)
- Partnerships (9)
- Rugged computing (9)
- Sales, Marketing, and Business Development (9)
- Trenton Systems (9)
- networking (9)
- Peripheral Component Interconnect Express (PCIe) (7)
- Encryption (6)
- Federal Information Processing Standards (FIPS) (6)
- GPUs (6)
- IPU (6)
- Joint All-Domain Command and Control (JADC2) (6)
- Server motherboards (6)
- artificial intelligence (6)
- Computer stress tests (5)
- Cross domain solutions (5)
- Mission-critical servers (5)
- Rugged mini PCs (5)
- AI (4)
- BIOS (4)
- CPU (4)
- Defense (4)
- Military primes (4)
- Mission-critical systems (4)
- Platform Firmware Resilience (PFR) (4)
- Rugged blade servers (4)
- containerization (4)
- data protection (4)
- virtualization (4)
- Counterfeit electronic parts (3)
- DO-160 (3)
- Edge servers (3)
- Firmware (3)
- HPC (3)
- Just a Bunch of Disks (JBOD) (3)
- Leadership (3)
- Navy (3)
- O-RAN (3)
- RAID (3)
- RAM (3)
- Revision control (3)
- Ruggedization (3)
- SATCOM (3)
- Storage servers (3)
- Supply chain (3)
- Tactical Advanced Computer (TAC) (3)
- Wide-temp computers (3)
- computers made in the USA (3)
- data transfer (3)
- deep learning (3)
- embedded computers (3)
- embedded systems (3)
- firmware security (3)
- machine learning (3)
- Automatic test equipment (ATE) (2)
- C6ISR (2)
- COTS (2)
- COVID-19 (2)
- CPUs (2)
- Compliance (2)
- Compute Express Link (CXL) (2)
- Computer networking (2)
- Controlled Unclassified Information (CUI) (2)
- DDR (2)
- DDR4 (2)
- DPU (2)
- Dual CPU motherboards (2)
- EW (2)
- I/O (2)
- Military standards (2)
- NVIDIA (2)
- NVMe SSDs (2)
- PCIe (2)
- PCIe 4.0 (2)
- PCIe 5.0 (2)
- RAN (2)
- SIGINT (2)
- SWaP-C (2)
- Software Guard Extensions (SGX) (2)
- Submarines (2)
- Supply chain security (2)
- TAA compliance (2)
- airborne (2)
- as9100d (2)
- chassis (2)
- data diode (2)
- end-to-end solution (2)
- hardware security (2)
- hardware virtualization (2)
- integrated combat system (2)
- manufacturing reps (2)
- memory (2)
- mission computers (2)
- private 5G (2)
- protection (2)
- secure by design (2)
- small form factor (2)
- software security (2)
- vRAN (2)
- zero trust (2)
- zero trust architecture (2)
- 3U BAM Server (1)
- 4G (1)
- 4U (1)
- 5G Frequencies (1)
- 5G Frequency Bands (1)
- AI/ML/DL (1)
- Access CDS (1)
- Aegis Combat System (1)
- Armed Forces (1)
- Asymmetric encryption (1)
- C-RAN (1)
- COMINT (1)
- Cloud-based CDS (1)
- Coast Guard (1)
- Compliance testing (1)
- Computer life cycle (1)
- Containers (1)
- D-RAN (1)
- DART (1)
- DDR5 (1)
- DMEA (1)
- Data Center Modular Hardware System (DC-MHS) (1)
- Data Plane Development Kit (DPDK) (1)
- Defense Advanced Research Projects (DARP) (1)
- ELINT (1)
- EMI (1)
- EO/IR (1)
- Electromagnetic Interference (1)
- Electronic Warfare (EW) (1)
- FIPS 140-2 (1)
- FIPS 140-3 (1)
- Field Programmable Gate Array (FPGA) (1)
- Ground Control Stations (GCS) (1)
- Hardware-based CDS (1)
- Hybrid CDS (1)
- IES.5G (1)
- ION Mini PC (1)
- IP Ratings (1)
- IPMI (1)
- Industrial Internet of Things (IIoT) (1)
- Industry news (1)
- Integrated Base Defense (IBD) (1)
- LAN ports (1)
- LTE (1)
- Life cycle management (1)
- Lockheed Martin (1)
- MIL-S-901 (1)
- MIL-STD-167-1 (1)
- MIL-STD-461 (1)
- MIL-STD-464 (1)
- MOSA (1)
- Multi-Access Edge Computing (1)
- NASA (1)
- NIC (1)
- NIC Card (1)
- NVMe (1)
- O-RAN compliant (1)
- Oil and Gas (1)
- Open Compute Project (OCP) (1)
- OpenRAN (1)
- P4 (1)
- PCIe card (1)
- PCIe lane (1)
- PCIe slot (1)
- Precision timestamping (1)
- Product life cycle (1)
- ROM (1)
- Raytheon (1)
- Remotely piloted aircraft (RPA) (1)
- Rugged computing glossary (1)
- SEDs (1)
- SIM Card (1)
- Secure boot (1)
- Sensor Open Systems Architecture (SOSA) (1)
- Small form-factor pluggable (SFP) (1)
- Smart Edge (1)
- Smart NIC (1)
- SmartNIC (1)
- Software-based CDS (1)
- Symmetric encryption (1)
- System hardening (1)
- System hardening best practices (1)
- TME (1)
- Tech Partners (1)
- Total Memory Encryption (TME) (1)
- Transfer CDS (1)
- USB ports (1)
- VMEbus International Trade Association (VITA) (1)
- Vertical Lift Consortium (VLC) (1)
- Virtual machines (1)
- What are embedded systems? (1)
- Wired access backhaul (1)
- Wireless access backhaul (1)
- accredidation (1)
- aerospace (1)
- air gaps (1)
- airborne computers (1)
- asteroid (1)
- authentication (1)
- autonomous (1)
- certification (1)
- cognitive software-defined radios (CDRS) (1)
- command and control (C2) (1)
- communications (1)
- cores (1)
- custom (1)
- customer service (1)
- customer support (1)
- data linking (1)
- data recording (1)
- ethernet (1)
- full disk encryption (1)
- hardware monitoring (1)
- heat sink (1)
- hypervisor (1)
- in-house technical support (1)
- input (1)
- integrated edge solution (1)
- international business (1)
- licensed spectrum (1)
- liquid cooling (1)
- mCOTS (1)
- microelectronics (1)
- missile defense (1)
- mixed criticality (1)
- moving (1)
- multi-factor authentication (1)
- network slicing (1)
- neural networks (1)
- new headquarters (1)
- next generation interceptor (1)
- non-volatile memory (1)
- operating system (1)
- output (1)
- outsourced technical support (1)
- post-boot (1)
- pre-boot (1)
- private networks (1)
- public networks (1)
- radio access network (RAN) (1)
- reconnaissance (1)
- rugged memory (1)
- secure flash (1)
- security (1)
- self-encrypting drives (SEDs) (1)
- sff (1)
- software (1)
- software-defined radios (SDRs) (1)
- speeds and feeds (1)
- standalone (1)
- storage (1)
- systems (1)
- tactical wide area networks (1)
- technical support (1)
- technology (1)
- third-party motherboards (1)
- troposcatter communication (1)
- unlicensed spectrum (1)
- volatile memory (1)
- vpx (1)
- zero trust network (1)
- January 2025 (1)
- November 2024 (1)
- October 2024 (1)
- August 2024 (1)
- July 2024 (1)
- May 2024 (1)
- April 2024 (3)
- February 2024 (1)
- November 2023 (1)
- October 2023 (1)
- July 2023 (1)
- June 2023 (3)
- May 2023 (7)
- April 2023 (5)
- March 2023 (7)
- December 2022 (2)
- November 2022 (6)
- October 2022 (7)
- September 2022 (8)
- August 2022 (3)
- July 2022 (4)
- June 2022 (13)
- May 2022 (10)
- April 2022 (4)
- March 2022 (11)
- February 2022 (4)
- January 2022 (4)
- December 2021 (1)
- November 2021 (4)
- September 2021 (2)
- August 2021 (1)
- July 2021 (2)
- June 2021 (3)
- May 2021 (4)
- April 2021 (3)
- March 2021 (3)
- February 2021 (8)
- January 2021 (4)
- December 2020 (5)
- November 2020 (5)
- October 2020 (4)
- September 2020 (4)
- August 2020 (6)
- July 2020 (9)
- June 2020 (11)
- May 2020 (13)
- April 2020 (8)
- February 2020 (1)
- January 2020 (1)
- October 2019 (1)
- August 2019 (2)
- July 2019 (2)
- March 2019 (1)
- January 2019 (2)
- December 2018 (1)
- November 2018 (2)
- October 2018 (5)
- September 2018 (3)
- July 2018 (1)
- April 2018 (2)
- March 2018 (1)
- February 2018 (9)
- January 2018 (27)
- December 2017 (1)
- November 2017 (2)
- October 2017 (3)
/Trenton%20Systems%20Circular%20Logo-3.png?width=50&height=50&name=Trenton%20Systems%20Circular%20Logo-3.png)
No Comments Yet
Let us know what you think